Obtaining value from GDPR with solutions that work for your bottom line.

Compliance with the GDPR regulations can be profitable when done right. Apart from saving on legal fees and avoiding customer attrition, you can also prevent issues and support your B2B data sales pitches. For that you need to cover all aspects which we look into below.
GDPR regulations have certainly been around for quite a while already. Naturally everybody in the business world is familiar with the basic ideas behind it and companies have implemented their compliance solutions. Is it sufficient? Very often all the business and technical aspects are not part of these. Have you missed any? Did you consider all those that have profit potential? Selected of the often neglected details will be mentioned below, others will be covered in next articles. You can consider this article as a MVP checklist.
Circling back to that profit – and not simply in terms of avoiding hefty fines, but those of added value. Having good processes in place along with assurance of security and speed creates competitive advantage for those who work with and share data with 3rd party companies. Ability to indisputably prove to your partners that your data is well handled and by using it they are not facing any GDPR breach risks serves as an additional bonus. One that is likely to shift the negotiations in your favour, as few companies bother to follow in-depth GDPR compliance recommendations and stick to basic requirements. You stand out for the win.
If you are using an external company to verify and enhance your GDPR-compliant solutions, then you can ask them to document how well your company is performing in this aspect (including the solutions they introduced). This makes it easier to verify the quality for your partners.
Keep in mind: analytics and security departments have contradicting goals
Whilst your analytics department is happy to keep as much data as possible, from the security team’s point of view: less is more. The less data, the more safety. Even if GDPR rules are in place, they will opt for minimising the data amount for a lower breach and/or leak risk. On the other hand the value data contain is substantial and you would miss out if you strictly followed the security department’s preference. Therefore you must strategise to reach the right balance between opportunity and risk. There are two main techniques associated with GDPR data and these are already impacting this balance.
Pseudonymisation (pseudo anonymisation)
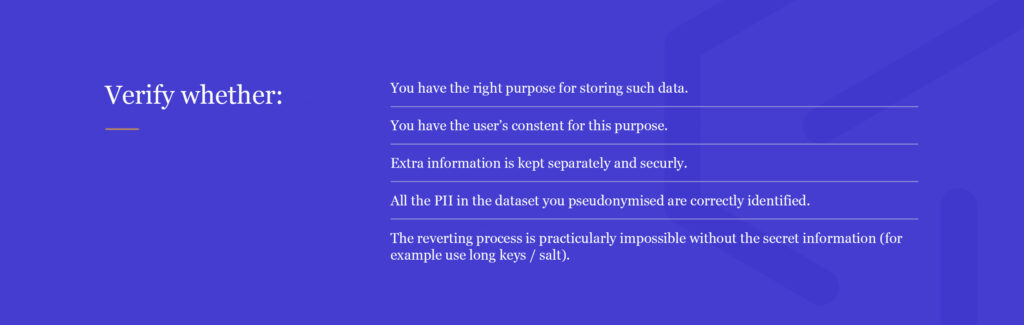
Pseudonymisation is a process which can be reverted with use of extra information, such as e.g. salt, encryption key. Using that information you can calculate which customer the data is associated with the pseudonymised data. It is a very fine method and many companies leverage it in some way. However, the key question is whether it is done right. You have to keep in mind a few key elements.
Bear in mind that it is very easy to identify fields which are obviously sensitive such as the name or a personal number. This often causes an illusion that PII seems an easy variable to spot. And it results in many companies missing those that do not seem sensitive at first glance. Such include those attributes that can be used to identify a single user when used in combination with other variables. More about that later on.
Pseudonymisation: pros & cons
Why choose pseudonymisation? Obviously you would like to be able to allow data analysts and data scientists to work with the data without exposing the personal information. This technique enables data scientists to e.g. come up with an upsell offer without seeing the personal information, thus meeting GDPR requirements. The key advantage of this approach is that it is reversible. This can be leveraged during offer send out, which at this particular step required the knowledge of which tailor made offer is best for which customer. Additionally this step can be fully automated. Subsequently, there is no need for data scientists to engage with the personal data.
The fact that pseudonymization is reversible can be used during offer send out – only at that step there is a need to know which customer to send the specific offer. And this step can be fully automated so there is no need of touching personal data by data scientists
Anonymisation:
Anonymisation is a process which is not reversible. This means that when working with anonymised data, one should never be able to identify an individual person based on the data. Yet again, there are a few aspects one must keep in mind when implementing it and during the approach selection process.
On one hand, anonymisation when done properly is significantly safer as a method. So it permits doing more with a company’s data. Even selling it to 3rd parties. However, it does limit your ability as a B2C provider. You will be unable to get insights and actions which are dedicated to an individual customer. Both of these hinge on correct implementation.
PII must be correctly identified and excluded, so that the anonymisation is not reversible. – Marcin Szymaniuk
The anonymisation should be 100% irreversible. Therefore, it is critical to properly analyse and identify all sets of attributes which can be used to identify a singular user. These must not be used. The reverse engineering could potentially happen after collecting an array of data points for many days. That’s why it’s important to go through careful analysis of all the data, including that which doesn’t belong to the sensitive field. For instance tracking the same customer for a long period of time could reveal his/her identity. The right analysis takes preemptive measures and will show all those that must be disallowed to present that. Disabling reverse engineering is particularly important for 3rd party players.
Anonymisation: advantages & drawbacks
Data presents a significant value. This is true for both internal use and for external partnerships. Business customers that purchase data want to safeguard against potential GDPR breach implications. As there is now a high competition amongst owners of big data, who wish to profit from sharing, it is important to stand out. 3rd party customers in particular can have more restrictive criteria. With truly ensured safety from breaches and impossible reverse engineering you become a strong competitor. And you are likely to make your security department more lenient in terms of amounts of data you get to keep, as this is a more secure method. Just as long as the implementation is done correctly.
A significant limitation of this method is the inability to target individual customers in your analysis and highly targeted personalised offers. Though it can be very useful for internal purposes as well. Such data still allows understanding trends and collecting insights about specific demographics and so on.
Final comments
GDPR compliance is a broad subject. Particularly when it comes to optimising the solutions for added value. This article has briefly covered the importance of analysis, particularly when it comes to variables that in combination with others enable identifying a single individual. There are multiple techniques, only two mentioned. More details and breadth will be covered in the upcoming articles. You can also expect subjects such as the multiple ways to approach the ‘right to be forgotten’ and ‘right to access’. So stay tuned.
Follow us on LinkedIn
